I heard the Confidential Computing term for the first time last week. I spent a couple of hours learning the basics this weekend and here is your summary. As I promised in the launch letter, it is at the 101 level, so you can learn the basics without spending so much effort.
The Problem
Let’s imagine!
We have a banking software. We have some sensitive data like bank accounts and transaction records and we have codes for the provided functionality in the software.
We run our software on machines in on-premise and the cloud. Our software stores data on disks and communicates with other instances via a network.
Data has 3 phases in this picture:
Data at rest (stored)
Data in use (in memory or in cpu)
Data in transit (in motion over the network)
We use encryption for data at rest and for data in transit since
Anyone shouldn’t be able to access our data (Confidentiality)
Anyone shouldn’t be able to change our data secretly (Integrity)
Even when they have access to disks or networks. Thanks to encryption, we can use an untrusted network to communicate or we can rent disks from others as long as we keep our encryption keys secret.
When it comes to data in use including the code, it is not encrypted in memory while being used.
Trust is good. Not trust is better
We trust everyone who can access that memory section like
our system admins
cloud-provider, its employees, and its all software
the operating system in the machine
all root software in the machine
That is why we have thousands of tools to manage ways to access our servers and why we don’t run our software on any server randomly.
That is why we carefully pick our cloud provider and hope they are not doing something wrong.
That is why it is not possible to use public clouds for some sensitive workloads and why some regulations forbid using public clouds.
Solution: Confidential computing with TEEs
Confidential computing is the name of the technology that aims to secure data in use by using Trusted Execution Environments.
A trusted execution environment (TEE) is a secure area of a CPU. It guarantees confidentiality and integrity of code/data. The codes in the TEE cannot be replaced or modified by unauthorized entities, which may also be the computer owner itself1.
The data in TEE is secured from the operating system/hypervisor, other software under our software in the stack, the cloud provider, and its employees.
Nice! Then we can run our software on any public cloud provider without worrying about the confidentiality of data in use. Right? What if they pretend to run our software with TEEs but they don’t?
Attestation
Attestation is an operation through which one software environment proves that a specific program is running on specific hardware.2
It is not easy to explain attestation and there are different ways to do it but I will simplify the procedure as much as possible to explain the idea behind it.3
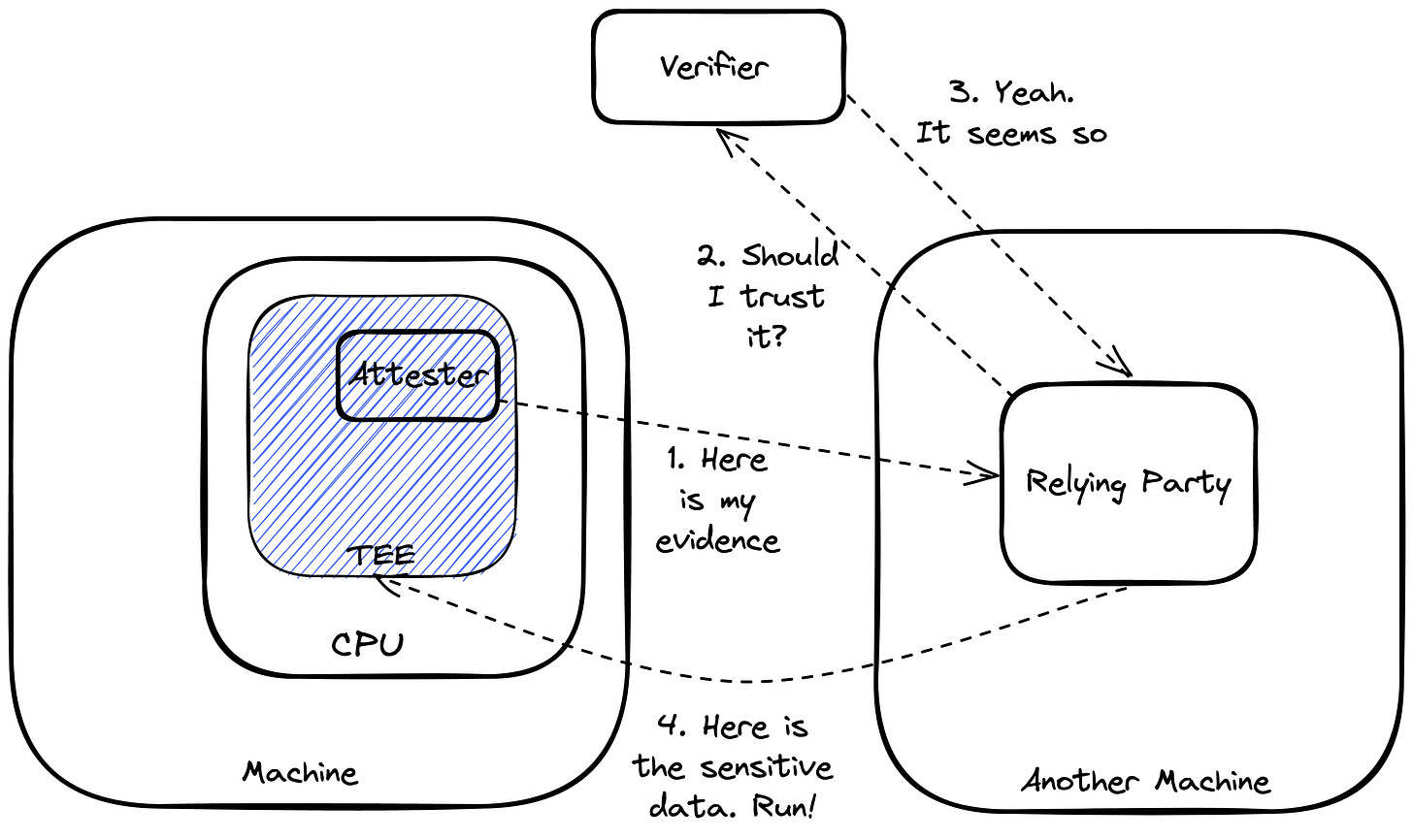
We have an “attester” which is an entity in TEE.
It collects some claims like key/value pairs about the state of the system.
It builds an evidence by using a set of claims.
It signs the evidence cryptographically.
We have a “relying party” in a remote machine.
It is like a client of the TEE environment.
It sends the evidence to the “verifier”.
If the evidence is verified by the “verifier”, it starts to trust the attester.
It shares sensitive data with the attester .
We have a trusted “verifier”
It trusts CPU manufacturers and it trusts public keys of manufacturers.
Based on predefined reference values, it verifies evidences.
And thanks to this procedure, we can ensure that our software runs on specific hardware like Intel SGX.
Without attestation, you’re not really doing Confidential Computing.4
Closing notes
As far as I understand, confidential computing is still a new technology and it is still maturing. Let's keep our eyes on this subject. It may be a mainstream practice in the future.
The Confidential Computing Consortium (CCC) brings together hardware vendors, cloud providers, and software developers to accelerate the adoption of Trusted Execution Environment (TEE) technologies and standards.
Confidential Containers is an open-source community working to enable cloud-native confidential computing by leveraging Trusted Execution Environments to protect containers and data.
Constellation is the first Confidential Kubernetes according to their claim.
https://en.wikipedia.org/wiki/Trusted_execution_environment
https://systex22.github.io/papers/systex22-final79.pdf
If you need more details, here are some good resources
- https://pradiptabanerjee.medium.com/understanding-attestation-process-in-a-confidential-computing-solution-ef8f876f34eb
- https://systex22.github.io/papers/systex22-final79.pdf
- https://ietf-rats-wg.github.io/architecture/draft-ietf-rats-architecture.html
https://aliceevebob.com/2022/06/14/what-is-attestation-for-confidential-computing/






Great read. Have you heard of enclaive.io. That open source project offers confidential compute container ready to use, incl. mariadb, mongodb, nginx etc. Building TEEs is very simple.
https://github.com/enclaive